TCP Server Connector
Version 24.3.9159
Version 24.3.9159
TCP Server Connector
TCP Server connectors support hosting a generic endpoint for receiving data over TCP.
Overview
Each TCP Server connector listens on a specified port for incoming TCP traffic, either with TLS/SSL encryption or plain text. Use this connector when CData Arc needs to receive arbitrary data that does not necessarily fit into the constraints provided by other standard protocols.
Since TCP traffic is a constant stream that does not intrinsically have a start or end point, you must configure the connector to determine where one message ends and the next begins. The connector supports two approaches:
- A static string/character delimiter that ends the current message or begins the next message
- Reading a value in the incoming TCP data to determine how long the message should be
For the second approach, the connector requires an offset (how many bytes after the first byte to begin reading the message length) and a size (how many bytes to read, starting at the offset, to get the length value). If the length of the message is the first value in the header for the message, the offset is 0.
Once the delimiter or length is reached, the connector pushes a message into the Arc flow containing the raw data received over TCP.
The TCP Server connector can also generate an Arc message when a client connects or disconnects, to alert other processes within the flow. See the Connected and Disconnected Messages section for more information.
For information on sending responses back to TCP clients, see the Sending Messages section.
Connector Settings
Settings Tab
Configuration
Settings related to the core configuration of the connector.
- Connector Id The static, unique identifier for the connector.
- Connector Type Displays the connector name and a description of what it does.
- Connector Description An optional field to provide a free-form description of the connector and its role in the flow.
- Port The port on which to listen for incoming TCP connections.
Message Decoding
Settings related to distinguishing individual messages from the TCP stream.
- Message Start Delimiter The character or string indicating the start of a new message.
- Message End Delimiter The character or string indicating the end of the current message.
- Message Length Offset The number of bytes to skip before beginning to read the length of the message from the incoming data.
- Message Length Size The size in bytes of the length value in the incoming data.
TLS Settings
Settings related to TLS/SSL transport security.
- Enable TLS Whether clients must negotiate TLS/SSL encryption to connect to the TCP server.
- Server Certificate The TLS/SSL certificate that identifies the TCP server.
- Certificate Password The password to access the server certificate’s private key.
Automation Tab
Automation
Settings related to the automatic processing of files by the connector.
- Send Whether messages arriving at the connector are automatically processed.
Performance
Settings related to the allocation of resources to the connector.
- Max Workers The maximum number of worker threads consumed from the threadpool to process files on this connector. If set, this overrides the default setting on the Settings > Automation page.
- Max Files The maximum number of files sent by each thread assigned to the connector. If set, this overrides the default setting on the Settings > Automation page.
Alerts Tab
Settings related to configuring alerts and Service Level Agreements (SLAs).
Connector Email Settings
Before you can execute SLAs, you need to set up email alerts for notifications. Clicking Configure Alerts opens a new browser window to the Settings page where you can set up system-wide alerts. See Alerts for more information.
Service Level Agreement (SLA) Settings
SLAs enable you to configure the volume you expect connectors in your flow to send or receive, and to set the time frame in which you expect that volume to be met. CData Arc sends emails to warn the user when an SLA is not met, and marks the SLA as At Risk, which means that if the SLA is not met soon, it will be marked as Violated. This gives the user an opportunity to step in and determine the reasons the SLA is not being met, and to take appropriate actions. If the SLA is still not met at the end of the at-risk time period, the SLA is marked as violated, and the user is notified again.
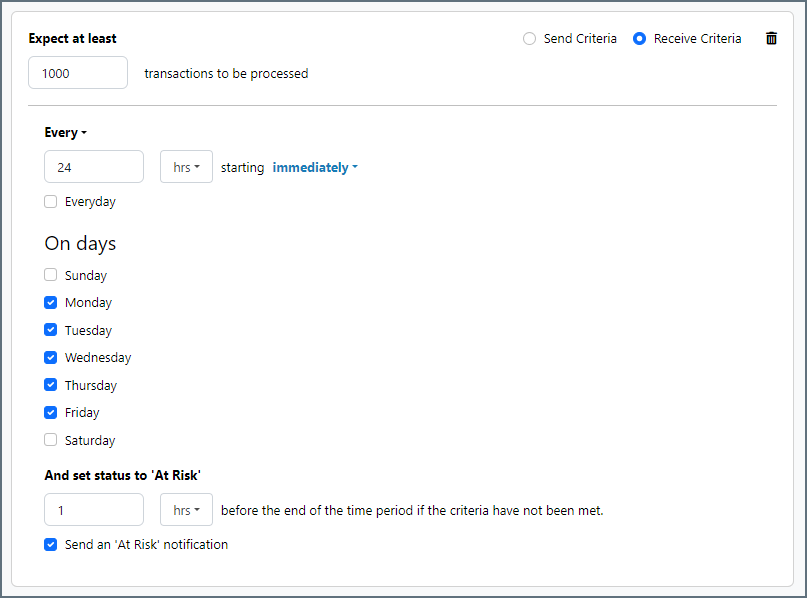
To define an SLA, click Add Expected Volume Criteria.
- If your connector has separate send and receive actions, use the radio buttons to specify which direction the SLA pertains to.
- Set Expect at least to the minimum number of transactions (the volume) you expect to be processed, then use the Every fields to specify the time frame.
- By default, the SLA is in effect every day. To change that, uncheck Everyday then check the boxes for the days of the week you want.
- Use And set status to ‘At Risk’ to indicate when the SLA should be marked as at risk.
- By default, notifications are not sent until an SLA is in violation. To change that, check Send an ‘At Risk’ notification.
The following example shows an SLA configured for a connector that expects to receive 1000 files every day Monday-Friday. An at-risk notification is sent 1 hour before the end of the time period if the 1000 files have not been received.
Advanced Tab
Keep Alive
Settings related to keep-alive packets sent by the server to maintain an idle connection.
- Keep Alive Whether to send keep-alive packets periodically to ensure that idle connections are not closed due to inactivity.
- Keep Alive Time The length of inactivity that should elapse before sending the first keep-alive packet.
- Keep Alive Interval The interval between consecutive keep-alive packets.
Advanced Settings
Settings not included in the previous categories.
- Connected Messages Whether the connector should generate an Arc message when a client connects. See the Connected and Disconnected Messages section for more information.
- Disconnected Messages Whether the connector should generate an Arc message when a client disconnects. See the Connected and Disconnected Messages section for more information.
- Idle Timeout The length of time (in seconds) the server should wait for an idle client before disconnecting them due to inactivity.
- Local File Scheme A scheme for assigning filenames to messages that are output by the connector. You can use macros in your filenames dynamically to include information such as identifiers and timestamps. For more information, see Macros.
- Local Host The binding address of the local server, if not the default network interface.
- Max Connections The maximum number of concurrent connectors.
- TLS Enabled Protocols The list of TLS/SSL protocols supported when establishing outgoing connections. Best practice is to only use TLS protocols. Some obsolete operating systems do not support TLS 1.2.
Message
- Save to Sent Folder Check this to copy files processed by the connector to the Sent folder for the connector.
- Sent Folder Scheme Instructs the connector to group messages in the Sent folder according to the selected interval. For example, the Weekly option instructs the connector to create a new subfolder each week and store all messages for the week in that folder. The blank setting tells the connector to save all messages directly in the Sent folder. For connectors that process many messages, using subfolders helps keep messsages organized and improves performance.
Logging
- Log Level The verbosity of logs generated by the connector. When you request support, set this to Debug.
- Log Subfolder Scheme Instructs the connector to group files in the Logs folder according to the selected interval. For example, the Weekly option instructs the connector to create a new subfolder each week and store all logs for the week in that folder. The blank setting tells the connector to save all logs directly in the Logs folder. For connectors that process many transactions, using subfolders helps keep logs organized and improves performance.
- Log Messages Check this to have the log entry for a processed file include a copy of the file itself. If you disable this, you might not be able to download a copy of the file from the Input or Output tabs.
Miscellaneous
Miscellaneous settings are for specific use cases.
- Other Settings Enables you to configure hidden connector settings in a semicolon-separated list (for example,
setting1=value1;setting2=value2). Normal connector use cases and functionality should not require the use of these settings.
Server Tab
Trusted IP Addresses
The following functions are available in the Trusted IP Addresses section:
- Add Enter a new IP address range.
- Edit Modify the selected IP address range.
- Delete Deletes the selected IP address range from the list.
The following restrictions apply to this feature:
localhostcannot be modified or removed from the list.- Any IP addresses outside of the defined ranges are rejected.
- Ranges are supported. For example, the entry
100.10.100.1-15indicates that IP addresses between100.10.100.1and100.10.100.15are allowed. - Classless inter-domain routing (CIDR) notation is supported. For example, the entry
100.10.100.0/24indicates that IP addresses between100.10.100.0and100.10.100.255are allowed. - Wildcard patterns are supported. For example, the entry
100.10.100.*indicates that IP addresses beginning with100.10.100are allowed.
Note: In order for clients to reach the server, a clear network path is required. In cloud environments you might need to make changes in three places:
- The networking rules in the cloud console.
- The firewall rules on the machine hosting the application. For example, when using an Amazon AMI, you might use an Uncomplicated Firewall (UFW) to allow traffic on the desired port. A common strategy in Linux environments is to forward traffic from ports lower than 1024 to a non-standard port higher than 1024, while configuring the application to use the non-standard port. This avoids permission issues associated with non-root users binding to ports lower than 1024.
- The Trusted IP Addresses portion of the Settings page.
Connected and Disconnected Messages
By default, the TCP Server connector only generates Arc messages when clients transfer data that the connector recognizes as a full message (according to the settings in the Message Decoding section). The connector can also generate Arc messages when a client connects to the server (if Connected Messages is enabled on the Advanced tab) or disconnects from the server (if Disconnected Messages is enabled on the Advanced tab).
When these special messages are generated, a special header is added to the Arc message:
x-tcpserver-event
This header is set to the value connected when clients are connecting, and disconnected when clients are disconnecting.
This header value must be checked by later connectors in the flow to detect whether a message written to the output folder of a TCP Server connector is one of these special messages.
Sending Messages
The TCP Server connector also uses a special header value to send messages back to connected clients:
x-tcpserver-connectionid
This header is added to any output messages generated by the connector, and is set to a Connection ID value that uniquely identifies the connected client. Messages that should be sent back to this client must have this header set to the same value to ensure that the message is sent to the appropriate client.
Since this header is already present on any messages written out by the connector, if the message passes through an Arc flow and arrives back at the Input for the TCP Server connector, it still has the same Connection ID value and is returned to the client that sent the original message. If the message cannot be directly routed back to the TCP Server connector, the Connection ID value must be saved and applied as a header (with the name shown above) to any new messages that should be returned to the client.
Macros
Using macros in file naming strategies can enhance organizational efficiency and contextual understanding of data. By incorporating macros into filenames, you can dynamically include relevant information such as identifiers, timestamps, and header information, providing valuable context to each file. This helps ensure that filenames reflect details important to your organization.
CData Arc supports these macros, which all use the following syntax: %Macro%.
| Macro | Description |
|---|---|
| ConnectorID | Evaluates to the ConnectorID of the connector. |
| Ext | Evaluates to the file extension of the file currently being processed by the connector. |
| Filename | Evaluates to the filename (extension included) of the file currently being processed by the connector. |
| FilenameNoExt | Evaluates to the filename (without the extension) of the file currently being processed by the connector. |
| MessageId | Evaluates to the MessageId of the message being output by the connector. |
| RegexFilename:pattern | Applies a RegEx pattern to the filename of the file currently being processed by the connector. |
| Header:headername | Evaluates to the value of a targeted header (headername) on the current message being processed by the connector. |
| LongDate | Evaluates to the current datetime of the system in long-handed format (for example, Wednesday, January 24, 2024). |
| ShortDate | Evaluates to the current datetime of the system in a yyyy-MM-dd format (for example, 2024-01-24). |
| DateFormat:format | Evaluates to the current datetime of the system in the specified format (format). See Sample Date Formats for the available datetime formats |
| Vault:vaultitem | Evaluates to the value of the specified vault item. |
| ConnectionId | Evaluates to the ConnectionId of the connection a client used to upload data. |
| RemoteHost | Evaluates to the ConnectionId of the connection that the client used to upload data. |
Examples
Some macros, such as %Ext% and %ShortDate%, do not require an argument, but others do. All macros that take an argument use the following syntax: %Macro:argument%
Here are some examples of the macros that take an argument:
- %Header:headername%: Where
headernameis the name of a header on a message. - %Header:mycustomheader% resolves to the value of the
mycustomheaderheader set on the input message. - %Header:ponum% resolves to the value of the
ponumheader set on the input message. - %RegexFilename:pattern%: Where
patternis a regex pattern. For example,%RegexFilename:^([\w][A-Za-z]+)%matches and resolves to the first word in the filename and is case insensitive (test_file.xmlresolves totest). - %Vault:vaultitem%: Where
vaultitemis the name of an item in the vault. For example,%Vault:companyname%resolves to the value of thecompanynameitem stored in the vault. - %DateFormat:format%: Where
formatis an accepted date format (see Sample Date Formats for details). For example,%DateFormat:yyyy-MM-dd-HH-mm-ss-fff%resolves to the date and timestamp on the file.
You can also create more sophisticated macros, as shown in the following examples:
- Combining multiple macros in one filename:
%DateFormat:yyyy-MM-dd-HH-mm-ss-fff%%EXT% - Including text outside of the macro:
MyFile_%DateFormat:yyyy-MM-dd-HH-mm-ss-fff% - Including text within the macro:
%DateFormat:'DateProcessed-'yyyy-MM-dd_'TimeProcessed-'HH-mm-ss%