SOAP Connector
Version 23.4.8841
Version 23.4.8841
SOAP Connector
SOAP connectors support sending SOAP messages to remote web services and retrieving the response.
Overview
The input to a SOAP connector should be the the full SOAP message to send to the web service. You can generate a template for the SOAP message by importing a WSDL for the target web service. Read the SOAP Templates section for details.
The SOAP connector supports HTTP Authentication, Token Authentication, and TLS Client Authentication, and can add digital encryption and signatures to the outgoing SOAP message for web service security. After sending the SOAP request, the connector stores the response or passes it along to the next connector in the CData Arc flow.
Connector Configuration
This section contains all of the configurable connector properties.
Settings Tab
Partner Info
Settings for identifying the target web service.
- Connector Id The static, unique identifier for the connector.
- Connector Type Displays the connector name and a description of what it does.
- Connector Description An optional field to provide a free-form description of the connector and its role in the flow.
- Service Endpoint The URL to which SOAP requests should be sent.
- SOAP Action The web service action to be triggered on the remote server.
- SOAP Version The version of SOAP you are using.
- Import from WSDL WSDLs can be imported from a URL or from a local file, and then automatically populate configuration fields in the connector. Importing a WSDL also allows for generating an XML template for SOAP requests when connected to an XML Map connector. See SOAP Templates for details.
WS-Security
Settings related to securing the web service transmissions.
- Send Message Security Whether to sign and/or encrypt outgoing SOAP requests.
- Receive Message Security Whether to require that signatures and encryption are present for incoming SOAP responses. An error is thrown if a received message does not have a required security parameter.
- Time To Live The length of time the connector waits for a connection response before throwing a timeout error.
Client Certificate
Settings related to the private local certificates.
- Private Certificate The private certificate used for signing outgoing requests and decrypting incoming responses.
- Certificate Password The password for accessing the private certificate.
Server Certificates
Settings related to the server’s public certificates.
- Encryption Certificate The public certificate used for encryption when sending messages and signature verification when receiving responses.
- TLS Server Certificate The public certificate used to verify the identity of an SSL/TLS server. Only required if you are sending requests over HTTPS (instead of HTTP). In the absence of a specific server certificate, you can leave this blank to allow the underlying OS/JVM to perform certificate validation, or you can set it to Any Certificate to trust the target server’s identity. Use Any Certificate with caution: the certificate verifies that you are connecting to the intended server.
Automation Tab
Automation Settings
Settings related to the automatic processing of files by the connector.
- Send Whether files arriving at the connector are automatically sent as SOAP requests.
- Retry Interval The amount of time before a failed send is retried. A retry is triggered when the server does not respond to a send attempt, or responds negatively to communicate that the file was not received.
- Max Attempts The maximum number of times the connector sends outgoing requests. Success is measured based on a successful server acknowledgement. If you set this to 0, the connector retries the request indefinitely.
Performance
Settings related to the allocation of resources to the connector.
- Max Workers The maximum number of worker threads consumed from the threadpool to process files on this connector. If set, this overrides the default setting on the Settings > Automation page.
- Max Files The maximum number of files sent by each thread assigned to the connector. If set, this overrides the default setting on the Settings > Automation page.
アラートタブ
アラートとサービスレベル(SLA)の設定に関連する設定.
コネクタのE メール設定
サービスレベル(SLA)を実行する前に、通知用のE メールアラートを設定する必要があります。アラートを設定をクリックすると、新しいブラウザウィンドウで設定ページが開き、システム全体のアラートを設定することができます。詳しくは、アラートを参照してください。
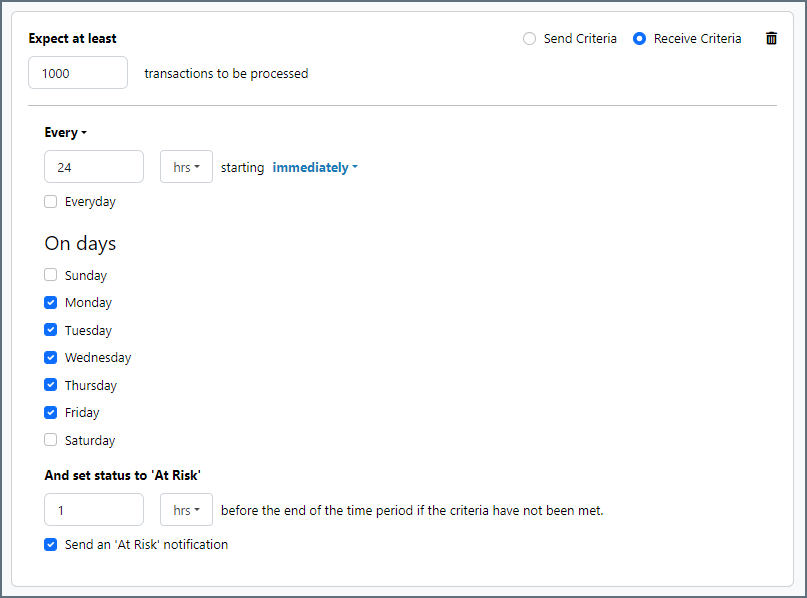
サービスレベル(SLA)の設定
サービスレベルでは、フロー内のコネクタが送受信すると予想される処理量を設定し、その量が満たされると予想される時間枠を設定できます。CData Arc は、サービスレベルが満たされていない場合にユーザーに警告するE メールを送信し、SLA を At Risk(危険) としてマークします。これは、サービスレベルがすぐに満たされない場合に Violated(違反) としてマークされることを意味します。これにより、ユーザーはサービスレベルが満たされていない理由を特定し、適切な措置を講じることができます。At Risk の期間内にサービスレベルが満たされなかった場合、SLA はViolated としてマークされ、ユーザーに再度通知されます。
サービスレベルを定義するには、予想処理量の条件を追加をクリックします。
- コネクタに個別の送信アクションと受信アクションがある場合は、ラジオボタンを使用してSLA に関連する方向を指定します。
- 検知基準(最小)を、処理が予想されるトランザクションの最小値(量)に設定し、毎フィールドを使用して期間を指定します。
- デフォルトでは、SLA は毎日有効です。これを変更するには、毎日のチェックをOFF にし、希望する曜日のチェックをON にします。
- 期間終了前にステータスを’At Risk’ に設定するタイミングを使用して、SLA がAt Risk としてマークされるようにします。
- デフォルトでは、通知はSLA が違反のステータスになるまで送信されません。これを変更するには、‘At Risk’ 通知を送信のチェックをON にします。
次の例は、月曜日から金曜日まで毎日1000ファイルを受信すると予想されるコネクタに対して構成されたSLA を示しています。1000ファイルが受信されていない場合、期間終了の1時間前にAt Risk 通知が送信されます。
Advanced Tab
Token Authentication
Settings related to token client authentication.
- Token Authentication Check this to enable token authentication for outgoing messages. If enabled, outgoing messages include the user credentials set below.
- Username The username required to access the token.
- Password The password required to access the token.
- Password Type Use the radio buttons to specify whether the password is in plain text (Text) or is encrypted (Digest).
TLS Client Authentication
Settings related to client authentication when two-way TLS authentication is required.
- Private Certificate The private certificate presented during TLS client authentication.
- Certificate Password The password required to access the TLS client certificate.
HTTP Authentication
Settings related to HTTP client authentication.
- Use HTTP Authentication Check this to enable client HTTP Authentication.
- HTTP Authentication Type Whether to provide HTTP authentication credentials in an encrypted format (Digest) or in plain text (Basic). Basic authentication should only be used if the the connection is an HTTPS connection (rather than HTTP).
- User The User credential for HTTP client authentication.
- Password The Password credential for HTTP client authentication.
Custom Headers
A set of custom headers to include as part of the outgoing message.
Proxy Settings
These are a collection of settings that identify and authenticate to the proxy through which the SOAP connection should be routed. By default, this section uses the global settings on the Settings Page. Clear the checkbox to supply settings specific to your SOAP connector.
- Proxy Type The protocol used by a proxy-based firewall.
- Proxy Host The name or IP address of a proxy-based firewall.
- Proxy Port The TCP port for a proxy-based firewall.
- Proxy User The user name to use to authenticate with a proxy-based firewall.
- Proxy Password A password used to authenticate to a proxy-based firewall.
- Authentication Scheme Leave the default None or choose from one of the following authentication schemes: Basic, Digest, Proprietary, or NTLM.
Advanced Settings
Settings not included in the previous categories.
- Connection Timeout The length of time the connector waits for a connection response before throwing a timeout error.
- Encryption Algorithm The algorithm to use when encrypting outgoing messages.
- Normalize Issuer Subject Whether certificate issuer data should be normalized into a simple string for validation by the web service.
- Processing Delay The amount of time (in seconds) by which the processing of files placed in the Input folder is delayed. This is a legacy setting. Best practice is to use a File connector to manage local file systems instead of this setting.
- Signature Algorithm The algorithm to use when signing outgoing messages. The same algorithm is requested for the corresponding MDN receipts.
- Sign Header Payload By default, the connector only signs the body of the SOAP message. Check this to have the connector also sign the headers.
- Security Token Format Determines the format used for security tokens in SOAP payloads.
X509 references contain the certificate subject in DN (distinguished name) format.
Binary tokens use the Base64 encoded contents of the entire public key.
KeyIdentifier references contain the X509 Subject-Key-Identifier format. - Local File Scheme A scheme for assigning filenames to messages that are output by the connector. You can use macros in your filenames dynamically to include information such as identifiers and timestamps. For more information, see Macros.
- TLS Enabled Protocols The list of SSL/TLS protocols supported when establishing outgoing connections. Best practice is to only use TLS protocols. Keep in mind that some obsolete operating systems do not support TLS 1.2.
- Verification Certificate The public certificate used to verify incoming SOAP responses. This field is only necessary if a different certificate should be used to verify signatures than the public certificate set in Encryption Certificate.
Message
- Save to Sent Folder Check this to copy files processed by the connector to the Sent folder for the connector.
- Sent Folder Scheme Instructs the connector to group messages in the Sent folder according to the selected interval. For example, the Weekly option instructs the connector to create a new subfolder each week and store all messages for the week in that folder. The blank setting tells the connector to save all messages directly in the Sent folder. For connectors that process many messages, using subfolders helps keep messsages organized and improves performance.
Logging
- Log Level The verbosity of logs generated by the connector. When you request support, set this to Debug.
- Log Subfolder Scheme Instructs the connector to group files in the Logs folder according to the selected interval. For example, the Weekly option instructs the connector to create a new subfolder each week and store all logs for the week in that folder. The blank setting tells the connector to save all logs directly in the Logs folder. For connectors that process many transactions, using subfolders helps keep logs organized and improves performance.
- Log Messages Check this to have the log entry for a processed file include a copy of the file itself. If you disable this, you might not be able to download a copy of the file from the Input or Output tabs.
Miscellaneous
Miscellaneous settings are for specific use cases.
- Other Settings Enables you to configure hidden connector settings in a semicolon-separated list (for example,
setting1=value1;setting2=value2). Normal connector use cases and functionality should not require the use of these settings.
Establishing a Connection
The Service Endpoint and Service Action for the target web service are required to establish a connection. Some web services might require one or more security features for SOAP requests:
- Encryption/Signing (WS-Security)
- Client SSL Authentication
- HTTP Authentication
SOAP Templates
The SOAP connector can simplify the process of generating SOAP requests through the use of a WSDL file and an XML Map connector that is connected to the SOAP connector in the flow. The WSDL file defines the appropriate XML structure for SOAP requests, and the XML Map connector can transform any XML structure into this target structure.
After using the Import WSDL button to import the file, connect an XML Map connector to the SOAP connector (so that files processed by the XML Map connector are then sent to the SOAP connector). After saving these flow changes, the XML Map connector can dynamically read the WSDL XML and use it as a Destination File template. Then, upload any source XML structure as the Source File in the XML Map connector.
After the Source File and Destination File are set in the XML Map connector, the visual designer is populated with the source and destination structures. Drag-and-drop elements from the source to the destination to map the relationship between the two XML structures. After the mapping is complete, files that match the Source File are automatically converted into SOAP requests by the XML Map connector.
Macros
Using macros in file naming strategies can enhance organizational efficiency and contextual understanding of data. By incorporating macros into filenames, you can dynamically include relevant information such as identifiers, timestamps, and header information, providing valuable context to each file. This helps ensure that filenames reflect details important to your organization.
CData Arc supports these macros, which all use the following syntax: %Macro%.
| Macro | Description |
|---|---|
| ConnectorID | Evaluates to the ConnectorID of the connector. |
| Ext | Evaluates to the file extension of the file currently being processed by the connector. |
| Filename | Evaluates to the filename (extension included) of the file currently being processed by the connector. |
| FilenameNoExt | Evaluates to the filename (without the extension) of the file currently being processed by the connector. |
| MessageId | Evaluates to the MessageId of the message being output by the connector. |
| RegexFilename:pattern | Applies a RegEx pattern to the filename of the file currently being processed by the connector. |
| Header:headername | Evaluates to the value of a targeted header (headername) on the current message being processed by the connector. |
| LongDate | Evaluates to the current datetime of the system in long-handed format (for example, Wednesday, January 24, 2024). |
| ShortDate | Evaluates to the current datetime of the system in a yyyy-MM-dd format (for example, 2024-01-24). |
| DateFormat:format | Evaluates to the current datetime of the system in the specified format (format). See サンプル日付フォーマット for the available datetime formats |
| Vault:vaultitem | Evaluates to the value of the specified vault item. |
Examples
Some macros, such as %Ext% and %ShortDate%, do not require an argument, but others do. All macros that take an argument use the following syntax: %Macro:argument%
Here are some examples of the macros that take an argument:
- %Header:headername%: Where
headernameis the name of a header on a message. - %Header:mycustomheader% resolves to the value of the
mycustomheaderheader set on the input message. - %Header:ponum% resolves to the value of the
ponumheader set on the input message. - %RegexFilename:pattern%: Where
patternis a regex pattern. For example,%RegexFilename:^([\w][A-Za-z]+)%matches and resolves to the first word in the filename and is case insensitive (test_file.xmlresolves totest). - %Vault:vaultitem%: Where
vaultitemis the name of an item in the vault. For example,%Vault:companyname%resolves to the value of thecompanynameitem stored in the vault. - %DateFormat:format%: Where
formatis an accepted date format (see サンプル日付フォーマット for details). For example,%DateFormat:yyyy-MM-dd-HH-mm-ss-fff%resolves to the date and timestamp on the file.
You can also create more sophisticated macros, as shown in the following examples:
- Combining multiple macros in one filename:
%DateFormat:yyyy-MM-dd-HH-mm-ss-fff%%EXT% - Including text outside of the macro:
MyFile_%DateFormat:yyyy-MM-dd-HH-mm-ss-fff% - Including text within the macro:
%DateFormat:'DateProcessed-'yyyy-MM-dd_'TimeProcessed-'HH-mm-ss%